Brocade SAN switches by default comes with four local user account( Figure 1).( root, factory,admin and user). Brocade SAN switches can be configured to authenticate with LDAP( Lightweight Directory Access Protocol) or windows Active directory services.
 |
To enable Brocade Fabric OS to authenticate with LDAP, Management port should be configured with IP and DNS servers. DNS address can be added to management port by “dnsconfig” Command.
Configuring DNSLogin to the switch with admin user and execute dnsconfig Admin> dnsconfig
Enter option
1 Display Domain Name Service (DNS) configuration 2 Set DNS configuration 3 Remove DNS configuration 4 Quit Select an item: (1..4) [4] 2
Type 2 and strike enter
Enter the Domain Name and DNS IP address:- Enter Domain Name: [] domain.com # Type your domain name and hit enter. Enter Name Server IP address in dot/colon notation: [] 192.168.1.1 # Type Primary DNS IP Enter Name Server IP address in dot/colon notation: [] 192.168.1.2 # Type Secondary DNS IP. DNS parameters saved successfully.
To integrate brocade SAN switch with LDAP or windows active directory management network should allowed to communicate with LDAP server on TCP port 389. Create a security group in windows active directory
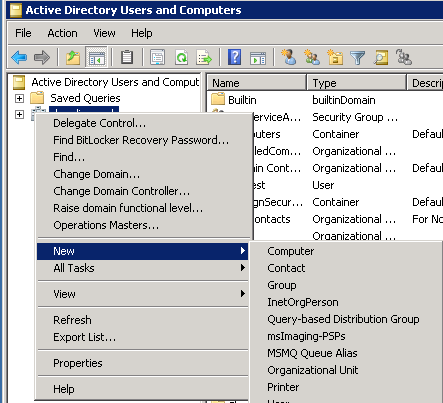
Login to the windows domain controller.Go to Start > Run and type "dsa.msc" . ( Alternatively start > Administrative tools > Active Directory Users and computers. )
Right click on the domain name> New > Group
Type the group name and click OK. Add the the users to this AD group
Add the domain controllers or LDAP servers to switchUse “aaaconfig” command to add the domain controllers : Add Primary Domain Controller :-“aaaconfig --add server1.domain.com -conf ldap -d Domain.com” Add Secondary Domain Controller-“aaaconfig --add server2.domain.com -conf ldap -d Domain.com”
Make LADP as primary authentication method
“aaaconfig --authspec "ldap;local"”
Map the LDAP group with Brocade admin role"ldapcfg --maprole brocade_admin admin"switch is ready for LDAP authendication. use user@domain format to login with the LDAP users.
|







This comment has been removed by the author.
ReplyDelete